AI Is Writing Our Code Faster Than We Can Verify It
This is the third article in a series on agentic engineering and AI-driven development. Read part one here, part two here, part three here, and look for the next article on April 23 on O’Reilly Radar. Here’s the dirty secret of the AI coding revolution: most experienced developers still don’t really trust the code the AI writes for […]
The Great CSS Expansion
A comprehensive look at how new CSS features are replacing JavaScript libraries. Anchor positioning, the Popover API, scroll-driven animations, view transitions, customizable selects, and more. The article estimates around 322 kB of JavaScript that can potentially be replaced by native CSS. Read more
datasette-ports 0.3
Release: datasette-ports 0.3 A small update for my tool for helping me figure out what all of the Datasette instances on my laptop are up to. Show working directory derived from each PID Show the full path to each database file Output now looks like this: http://127.0.0.1:8007/ - v1.0a26 Directory: /Users/simon/dev/blog Databases: simonwillisonblog: /Users/simon/dev/blog/simonwillisonblog.db Plugins: datasette-llm datasette-secrets http://127.0.0.1:8001/ - v1.0a26 Directory:…
Zig 0.16.0 release notes: "Juicy Main"
Zig 0.16.0 release notes: "Juicy Main" Zig has really good release notes - comprehensive, detailed, and with relevant usage examples for each of the new features. Of particular note in the newly released Zig 0.16.0 is what they are calling "Juicy Main" - a dependency injection feature for your program's main() function where accepting a process.Init parameter grants access to a struct of useful properties: const std = @import("std"); pub fn main(init: std.process.Init) !void { ///…
datasette PR #2689: Replace token-based CSRF with Sec-Fetch-Site header protection
datasette PR #2689: Replace token-based CSRF with Sec-Fetch-Site header protection Datasette has long protected against CSRF attacks using CSRF tokens, implemented using my asgi-csrf Python library. These are something of a pain to work with - you need to scatter forms in templates with <input type="hidden" name="csrftoken" value="{{ csrftoken() }}"> lines and then selectively disable CSRF protection for APIs that are intended to be called from outside the browser. I've been following…
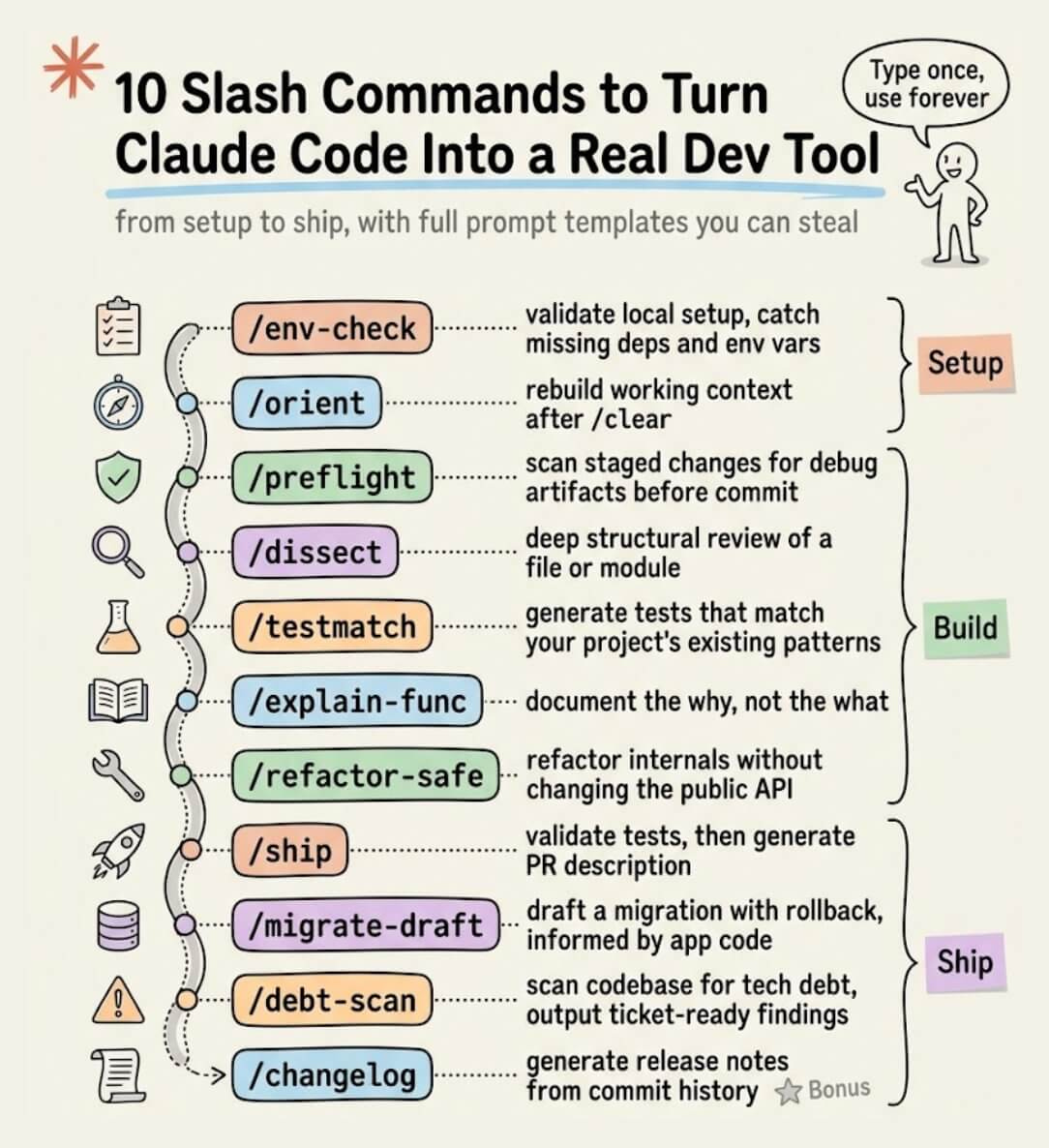
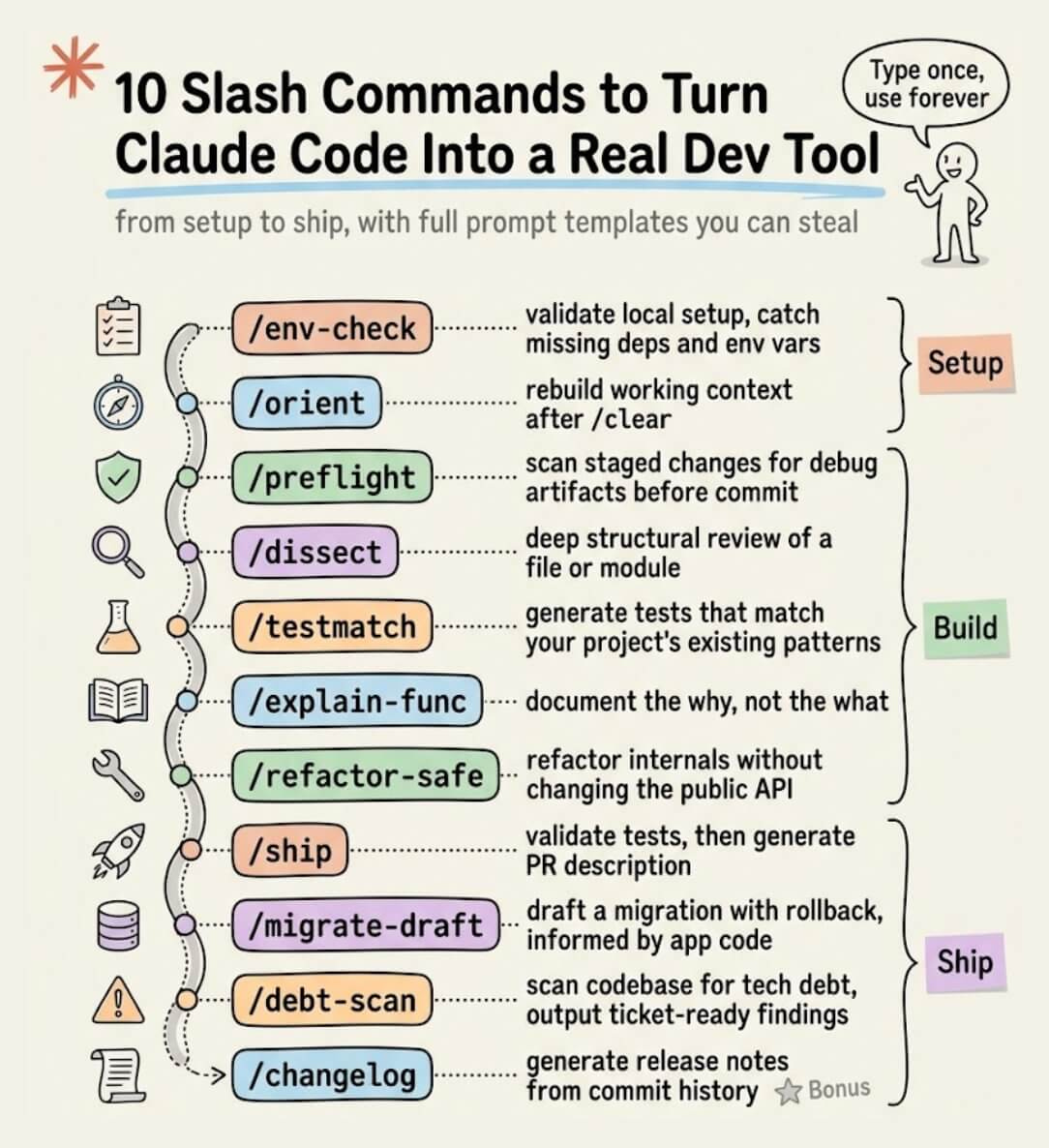
10 Must-use Slash Commands in Claude Code
...explained with exact prompts and usage!
Trusted access for the next era of cyber defense
Trusted access for the next era of cyber defense OpenAI's answer to Claude Mythos appears to be a new model called GPT-5.4-Cyber: In preparation for increasingly more capable models from OpenAI over the next few months, we are fine-tuning our models specifically to enable defensive cybersecurity use cases, starting today with a variant of GPT‑5.4 trained to be cyber-permissive: GPT‑5.4‑Cyber. They're also extending a program they launched in February (which I had missed) called Trusted Access…

Putting APIs to the Test
Welcome to the March edition of PHP Architect. We are excited to share ideas that will make you think and may even change some of your current practices. While we publish a magazine, we are developers first. We are experiencing the AI wave that many of you are also dealing with. There are new questions, […] The post Putting APIs to the Test appeared first on PHP Architect.
Cybersecurity Looks Like Proof of Work Now
Cybersecurity Looks Like Proof of Work Now The UK's AI Safety Institute recently published Our evaluation of Claude Mythos Preview’s cyber capabilities, their own independent analysis of Claude Mythos which backs up Anthropic's claims that it is exceptionally effective at identifying security vulnerabilities. Drew Breunig notes that AISI's report shows that the more tokens (and hence money) they spent the better the result they got, which leads to a strong economic incentive to spend as much as…
Feross on the 10 Minutes or Less Podcast: Nobody Reads the Code
In the past few weeks alone, we’ve seen a surge in supply chain attacks, increasingly sophisticated social engineering, and even nation-state actors targeting maintainers. What used to feel like a niche concern is now a daily reality for teams building with open source. In this conversation, Socket CEO Feross Aboukhadijeh joins 10 Minutes or Less, a podcast by Ali Rohde, General Partner at Outset Capital, to break down what’s happening right now, from how the Axios backdoor attack unfolded to…

Symfony_Live Berlin: "Build Applications that Welcome Change"
We’re excited to announce that SymfonyLive Berlin 2026 will take place April 23–24, 2026 at CineStar CUBIX Alexanderplatz, right in the heart of Berlin, directly on Alexanderplatz and easily accessible by public transport. 🎤 New talk announcement!…

SymfonyLive Berlin 2026: "Specing out teamwork”
We’re excited to announce that SymfonyLive Berlin 2026 will take place April 23–24, 2026 at CineStar CUBIX Alexanderplatz, right in the heart of Berlin, directly on Alexanderplatz and easily accessible by public transport. 🎤 New talk at SymfonyLive…

Claude Mythos #3: Capabilities and Additions
To round out coverage of Mythos, today covers capabilities other than cyber, and anything else additional not covered by the first two posts, including new reactions and details.
Grief and the Nonprofessional Programmer
I can’t claim to be a professional software developer—not by a long shot. I occasionally write some Python code to analyze spreadsheets, and I occasionally hack something together on my own, usually related to prime numbers or numerical analysis. But I have to admit that I identify with both of the groups of programmers that […]
datasette PR #2689: Replace token-based CSRF with Sec-Fetch-Site header protection




How 10x Developers Actually Use AI
AI Is Writing Our Code Faster Than We Can Verify It
The Great CSS Expansion
datasette-ports 0.3
Zig 0.16.0 release notes: "Juicy Main"
datasette PR #2689: Replace token-based CSRF with Sec-Fetch-Site header protection
10 Must-use Slash Commands in Claude Code
Trusted access for the next era of cyber defense
Putting APIs to the Test
Cybersecurity Looks Like Proof of Work Now
Feross on the 10 Minutes or Less Podcast: Nobody Reads the Code
Symfony_Live Berlin: "Build Applications that Welcome Change"
SymfonyLive Berlin 2026: "Specing out teamwork”
Claude Mythos #3: Capabilities and Additions
Grief and the Nonprofessional Programmer
Aucun résultat
Essayez avec d'autres termes de recherche.